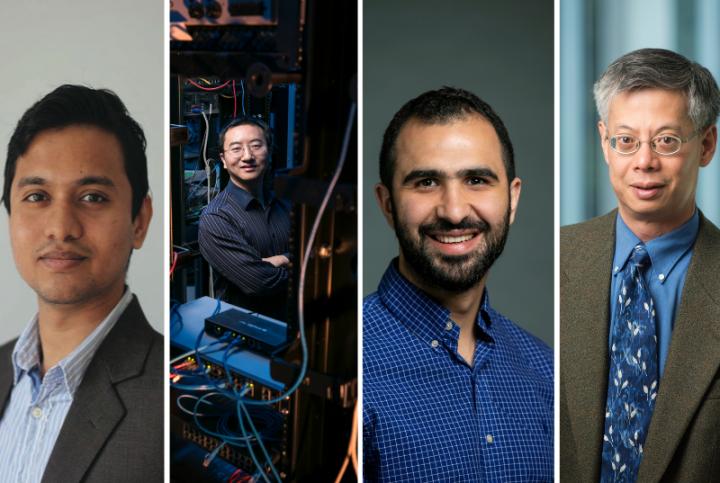
Credit: courtesy photo
The capabilities and reach of 5G are expanding, but with new capabilities come new security challenges. Four Mason Engineering researchers received a $1.6 million grant from DARPA to tackle one of the many security issues that 5G poses as part of a larger DARPA initiative called Open, Programmable, Secure 5G (OPS-5G).
The grant, entitled EPIC SWaPD: Energy Preserving Internet of Things (IoT) Cryptography for Small Weight and Power Devices, aims to optimize the security and energy efficiency tradeoff by creating a low-energy security architecture for various types of IoT devices.
“In a network, there are many different devices of different sizes and capabilities. Many of these devices don’t have much computing power or battery life, and a common cybersecurity attack on these devices is to drain their battery life,” says Brian Mark, co-principal investigator on the grant.
Mark,?Khaled Khasawneh,?Kai Zeng, and?Sai Manoj Pudukotai Dinakarrao in the Department of Electrical and Computer Engineering are collaborating with the company Kryptowire and Assistant Professor Matthew Hicks from Virginia Tech for the project.
These small IoT devices could be as simple as a thermometer or humidity sensor that is part of a larger smart home system. “These sensors can be very tiny, and they have limited computation and communication capabilities. The first step for each of these types of sensors would be to bootstrap, or link, a secure connection to the network, which requires authentication without pre-shared secrets. This is where the vulnerabilities lie,” says Kai Zeng.
When sensors or other types of small IoT devices must automatically authenticate themselves, attackers have many paths of attack. They can drain the device’s battery, rendering it useless, or steal sensitive information or data from the device. Because of the many pathways that attackers could use to harm these devices, the team is combining cryptography, network protocol design, and machine learning to assure the success and scalability of their efforts.
“Something really important for this effort is that the security architecture operates on the principles of zero trust and least privilege,” says Mark. “Zero trust means that when a device comes in and wants to join the network, the assumption is that there is no prior trust or information shared between the devices, while least privilege implies the minimum permissions are granted to the entity to perform its task. So, we needed to bootstrap the security association and grant an entity just enough authority to access the devices or data that it needs but no more than that.”
One way they are looking at securing the connection is through gait-inspired authentication, which leverages the kinetic energy generated by a human user. “Every device harvests energy in a different way, and we use the harvesting pattern for authentication of the device, which preserves energy and accomplishes a security task at the same time,” says Dinakarrao.
Another approach is to exploit the “always-on” sensors in some devices like smartphones. “We plan to employ always-on sensing to perform the exchange of device identification and cryptographic material,” says Khasawneh.
They are also using machine learning to ensure both authentication and authorization of different devices. “We not only have to authenticate the devices and entities that are allowed on a network, but we have to verify their different roles and privileges. I might be granted access to the information that tells me the temperature of a room, but perhaps I might not have the authorization to change the thermostat setting,” says Mark. “Using graph-based models, we can verify the trust relationships of different devices or entities and this process can be accelerated using machine learning techniques,” adds Dinakarrao.
Long-term, the team aspires for their security architecture to easily be applied to other devices. “When we talk about the energy and security tradeoff, we have to think about how we can do things in a smart way to conserve energy while enhancing security. But we also need to think about how to make our architecture scalable to larger, more geographically distributed networks. Right now, this work is with smaller devices, but the hope is that our overall security architecture can apply to a variety of devices with different capabilities,” says Mark.
###
Media Contact
Martha Bushong
[email protected]
Original Source
https:/




