Credit: NJIT
WASHINGTON (July 14, 2020)–Smartphone owners who unlock their devices with knock codes aren’t as safe as they think, according to researchers from New Jersey Institute of Technology, the George Washington University and Ruhr University Bochum.
Knock codes work by letting people select patterns to tap on a phone’s locked screen. LG popularized the method in 2014, and now there are approximately 700,000 people using this method in the U.S. alone, along with one million downloads worldwide of clone applications for Google Android devices generally, the researchers said.
Raina Samuel, a doctoral student in computer science at NJIT’s Ying Wu College of Computing, said she had the idea for this research while attending a security conference in 2017.
“During that conference I heard our co-author Adam Aviv give a presentation. He was talking about passwords, PINs, shoulder surfing and how these mobile methods of authentication can be manipulated and insecure sometimes,” she said. “At the time, I had an LG phone and I was using the knock codes. It was a bit of a personal interest for me.”
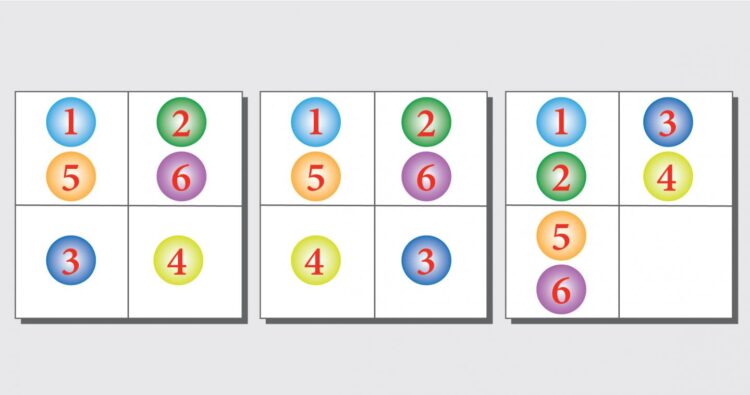
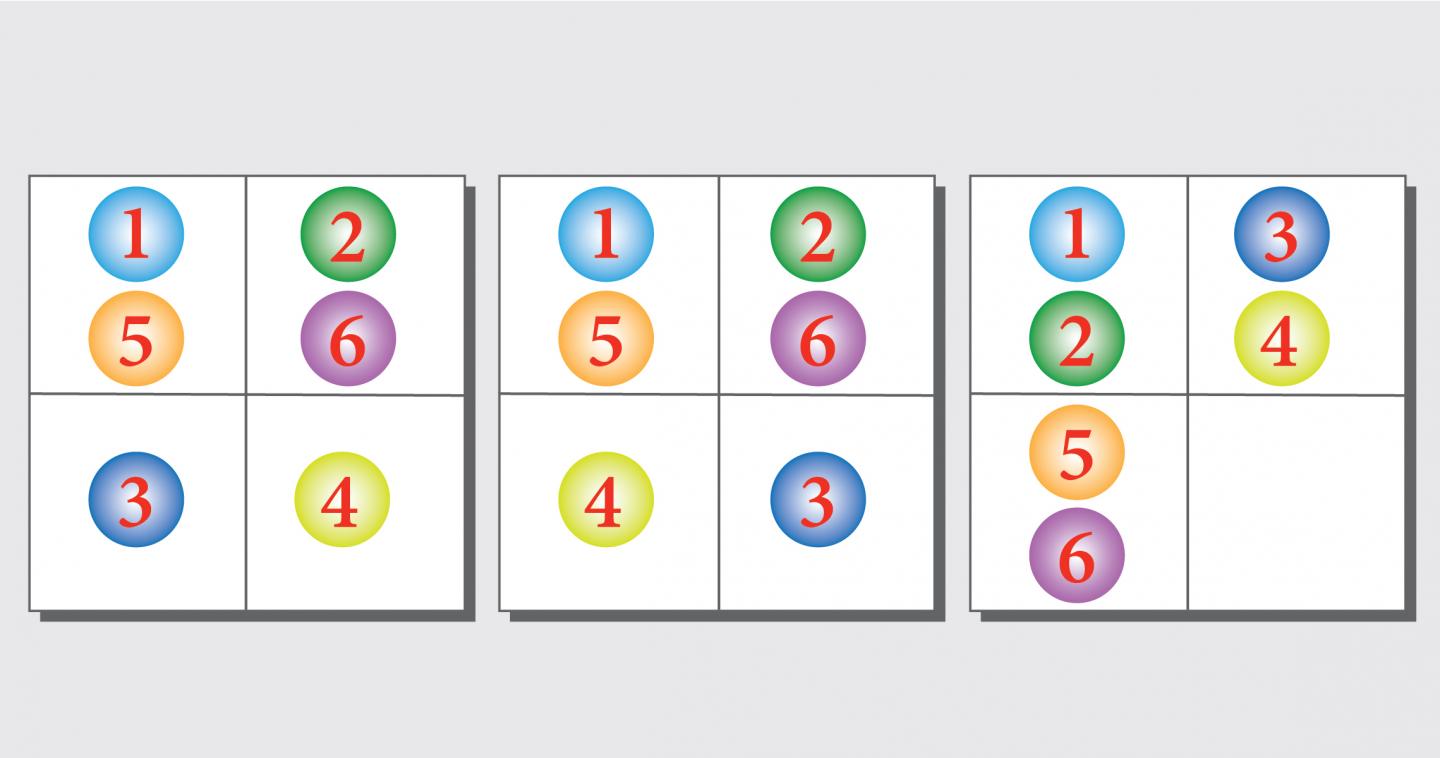
Knock codes typically present users with a 2-by-2 grid, which must be tapped in the correct sequence to unlock their phone. The sequence is between six and ten taps. The researchers analyzed how easily an attacker could guess a tapping pattern.
In an online study, 351 participants picked codes. The researchers found that 65% of users started their codes in the top left corner, often proceeding to the top right corner next, which could be attributed to Western reading habits. They also found that increasing the size of the grid didn’t help, instead making the users more likely to pick shorter codes.
“Knock codes really intrigued me as I have spent a lot of time working on other mobile authentication options, such as PINs or Android patterns, and had never heard of these,” Aviv, an associate professor of computer science at GW, said. “Turns out, while less popular than PINs or patterns, there are still a surprising number of people using knock codes, so it’s important to understand the security and usability properties of them.”
The researchers also tested a blocklist of common codes, so that survey participants would pick something harder to guess. The list contained the 30 most popular codes. The first three were:
- Top left, top right, bottom left, bottom right, top left, top right (Hourglass shape)
- Top left, top right, bottom right, bottom left, top left, top right (Square shape)
- Top left, top left, top right, top right, bottom left, bottom left. (Number 7 shape)
The researchers said there should be a feature that blocks codes which are too easy to guess and advises users to pick stronger ones, similar to how some websites respond when users create password-protected accounts.
The study showed that knock codes are difficult to memorize. Approximately one in ten participants forgot their code by the end of the study, even though it lasted only five minutes. In addition, entering such a code to unlock the display took 5 seconds on average, compared to entering a PIN which typically takes 4.5 seconds and an Android unlock pattern needing only 3 seconds.
The research team also included Ruhr University’s Philipp Markert. Aviv asked Markert to join their project when peer reviewers said the study of knock code patterns should be done on phones, not on computer simulations. Markert adapted the study’s programming for this change.
“I’m always interested in new authentication schemes, and I worked with Adam on a similar project about PINs, so when he asked me to join the team, I didn’t think twice.” Markert said.
The paper will be presented at the 16th Symposium on Usable Privacy and Security, held concurrently with the prestigious USENIX Security Symposium August 9-11. Funding was supplied by the Army Research Laboratory, National Science Foundation and Germany’s North Rhine-Westphalian Experts on Research in Digitalization.
###
Media Contact
Timothy Pierce
[email protected]